Trusted by companies all over the world

Operational Insights
Everything you need to optimize frontline operations
What you don’t know is hurting you. Parsable provides manufacturing and industrial leaders a deeper look into their operational inefficiencies with insights into how to fix them.
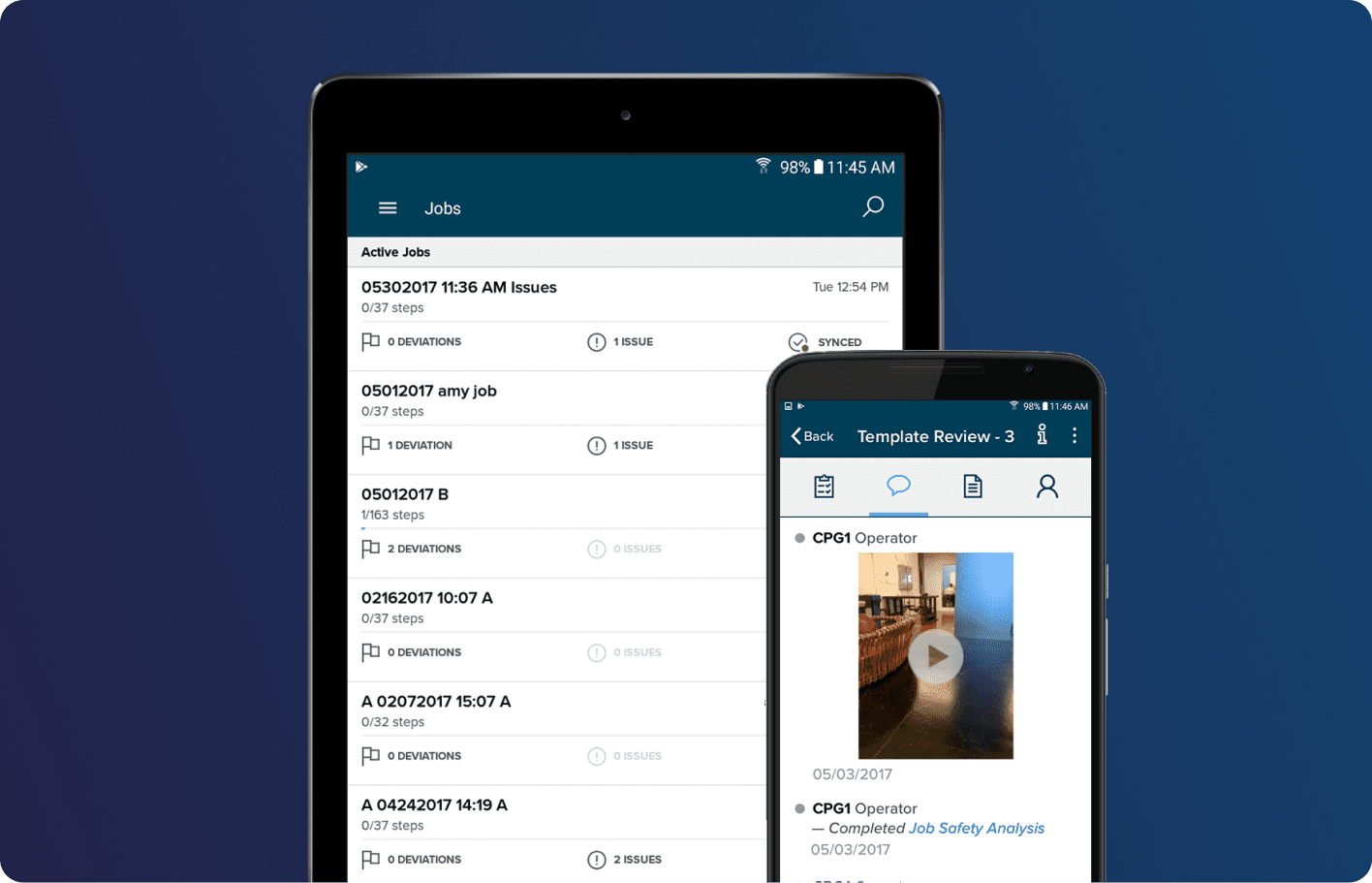
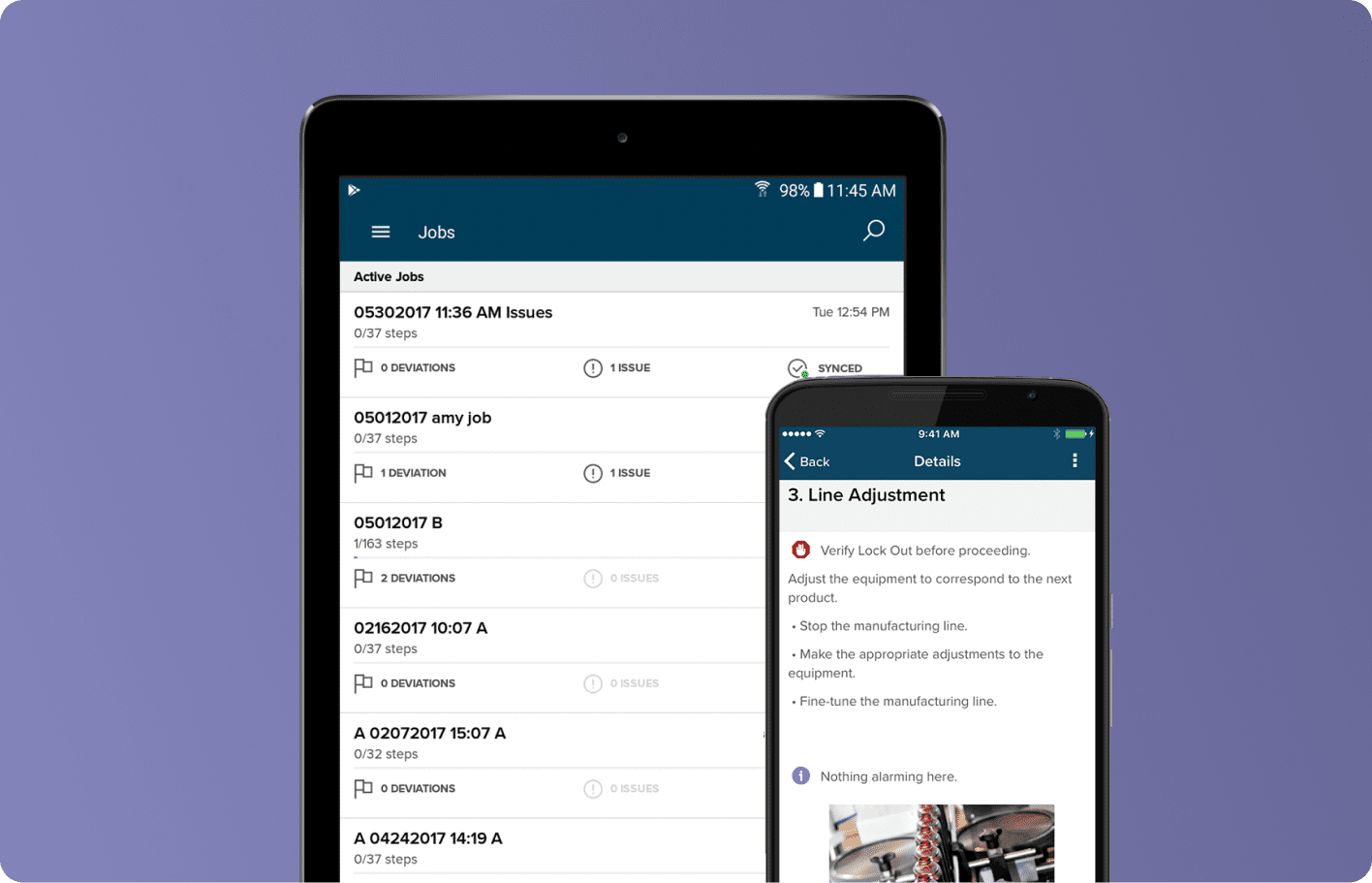
Digitize your frontline
Create, update, and distribute digital work instructions worldwide with an easy-to-use authoring tool. Capture and generate work execution data and insights through Parsable’s mobile app for industrial operations.
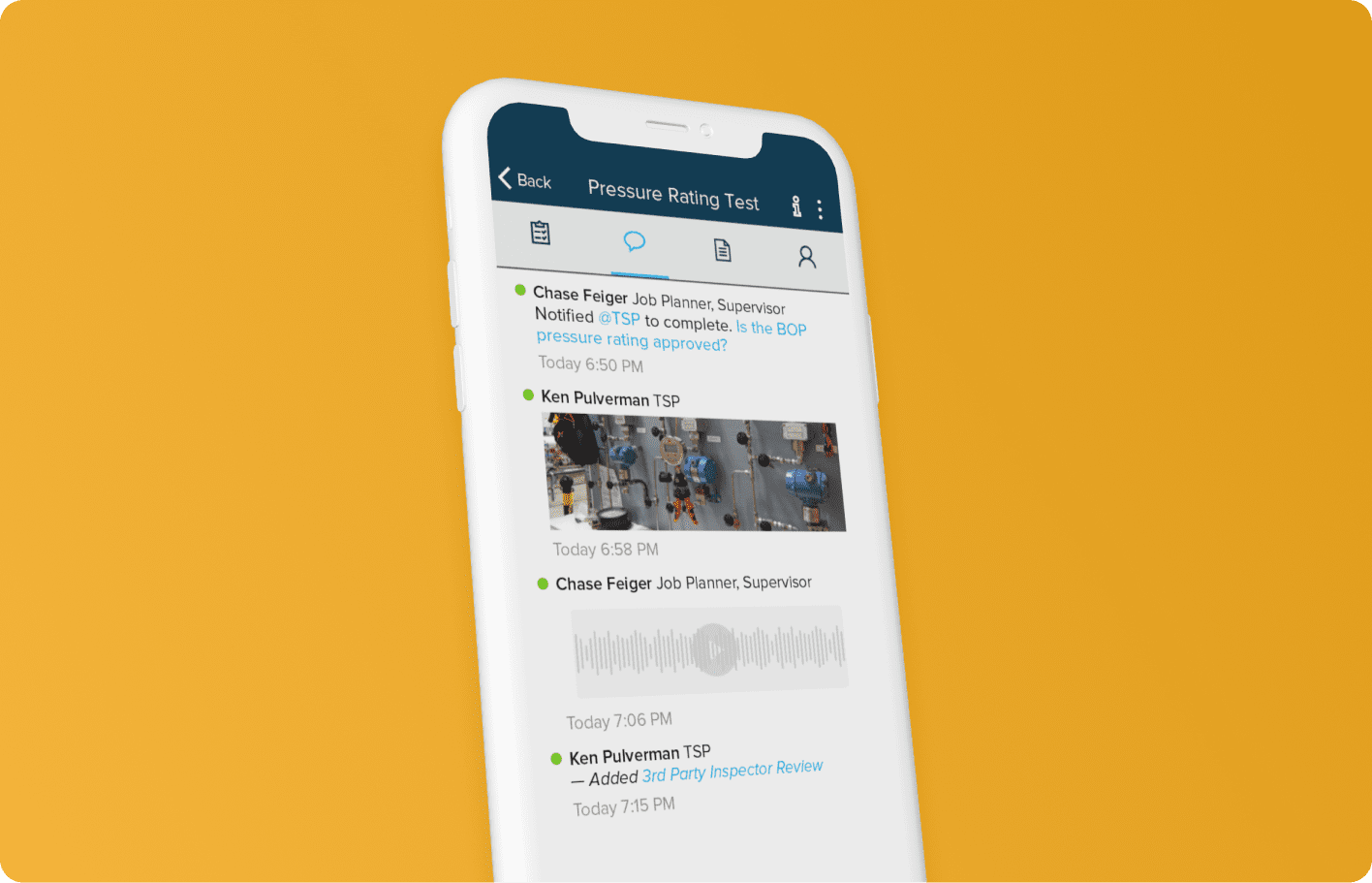
Engage your workforce
Enable collaboration amongst your teams. Post a question, report an issue, or share expertise through assignment-specific messaging portals.
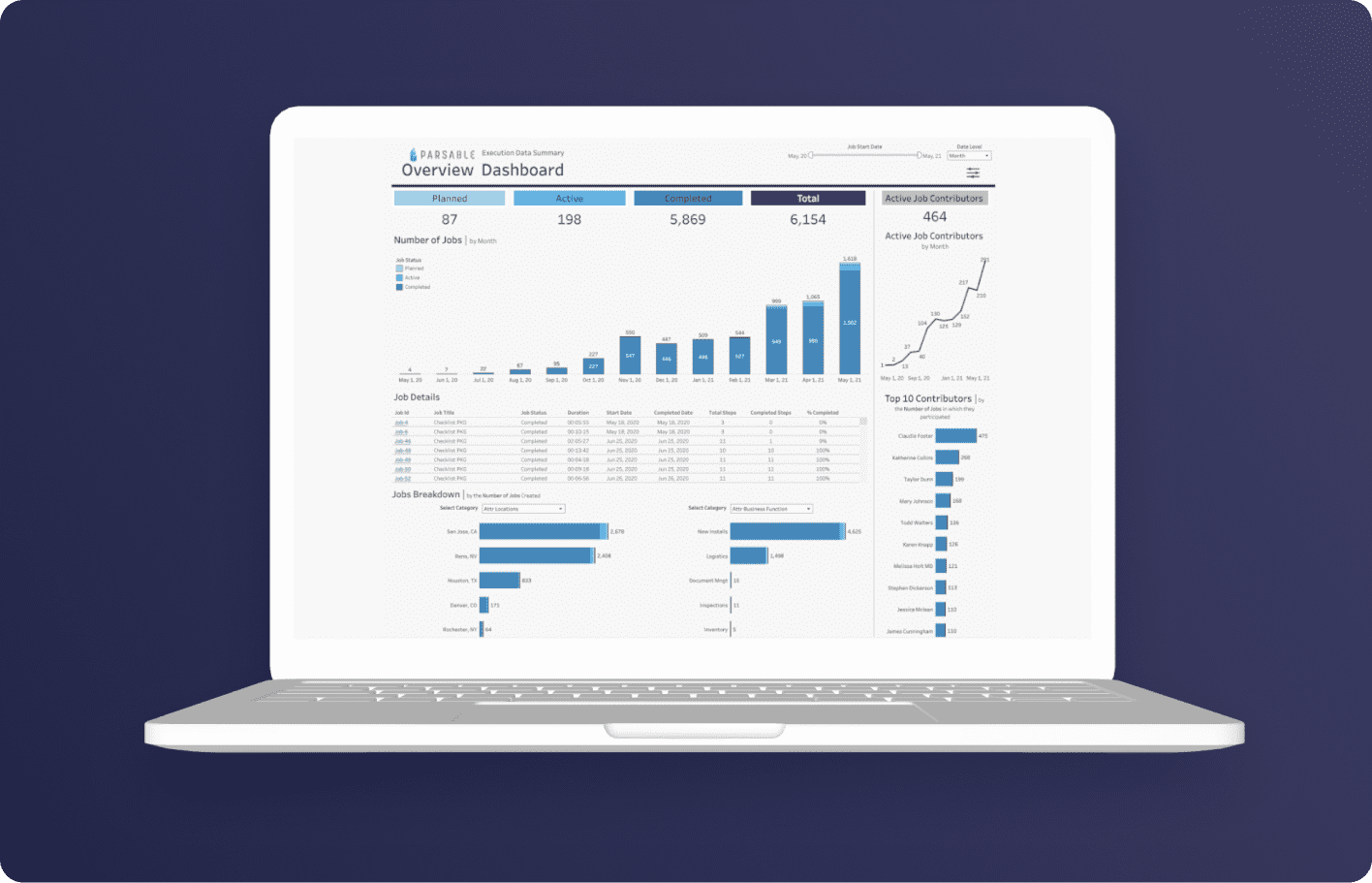
Unlock activity data
Leverage near real-time data to unlock actionable insights into inefficiencies impacting operational results. Use flexible configuration options to classify your data for easier organization storage, and analysis.
Transform your operations
Achieve impressive results by enabling your workforce to identify, implement, and sustain improvements – continuously.
Audits & Inspections
Automate the processing and tracking of all data associated with your frontline’s routine audits, inspections, checklists, and more.
Workflow & Collaboration
Enable frontline teams to work together more efficiently to shorten the time required for line changeovers, plant turnarounds, shift handoffs, and more.
Compliance & Adherence
Make your frontline operations audit proof by ensuring that what needs to get done always gets done.
On-the-Job Training
Spread expertise by upskilling workers in the moment with just-in-time learning, one-point lessons, and data-backed best practices.
Real-Time Integrations
Update your business-critical systems in real time and build resiliency, adaptability, and agility into your frontline operations.
Insights & Process Optimization
Unlock insights into inefficiencies impacting frontline processes and workflows, then take action to continuously improve frontline operations.






Operational Insights
Connect your teams and drive operational excellence

Industrial executives and leaders
Leverage human work execution data to improve operations and build a sustainable future.

Functional experts
Create, test, deploy, and improve critical SOPs with a no-code platform.

Frontline workers and supervisors
Learn, work, and collaborate across digital business processes to always get work done right.